Day 5 - Apktool
Writer: Karoliina Kemppainen
This Christmas we will be tweeting and blogging one useful CSIRT tool each day, thanking its makers and maintainers.
Today’s tool is Apktool which was originally created by Ryszard Wiśniewski and currently maintained by Connor Tumbleson. Thanks for creating this awesome tool!
Apktool is “a tool for reverse engineering 3rd party, closed, binary Android apps. It can decode resources to nearly original form and rebuild them after making some modifications. It also makes working with an app easier because of the project like file structure and automation of some repetitive tasks like building apk, etc. It is NOT intended for piracy and other non-legal uses. It could be used for localizing, adding some features or support for custom platforms, analyzing applications and much more.” (Quote from: https://ibotpeaches.github.io/Apktool/)
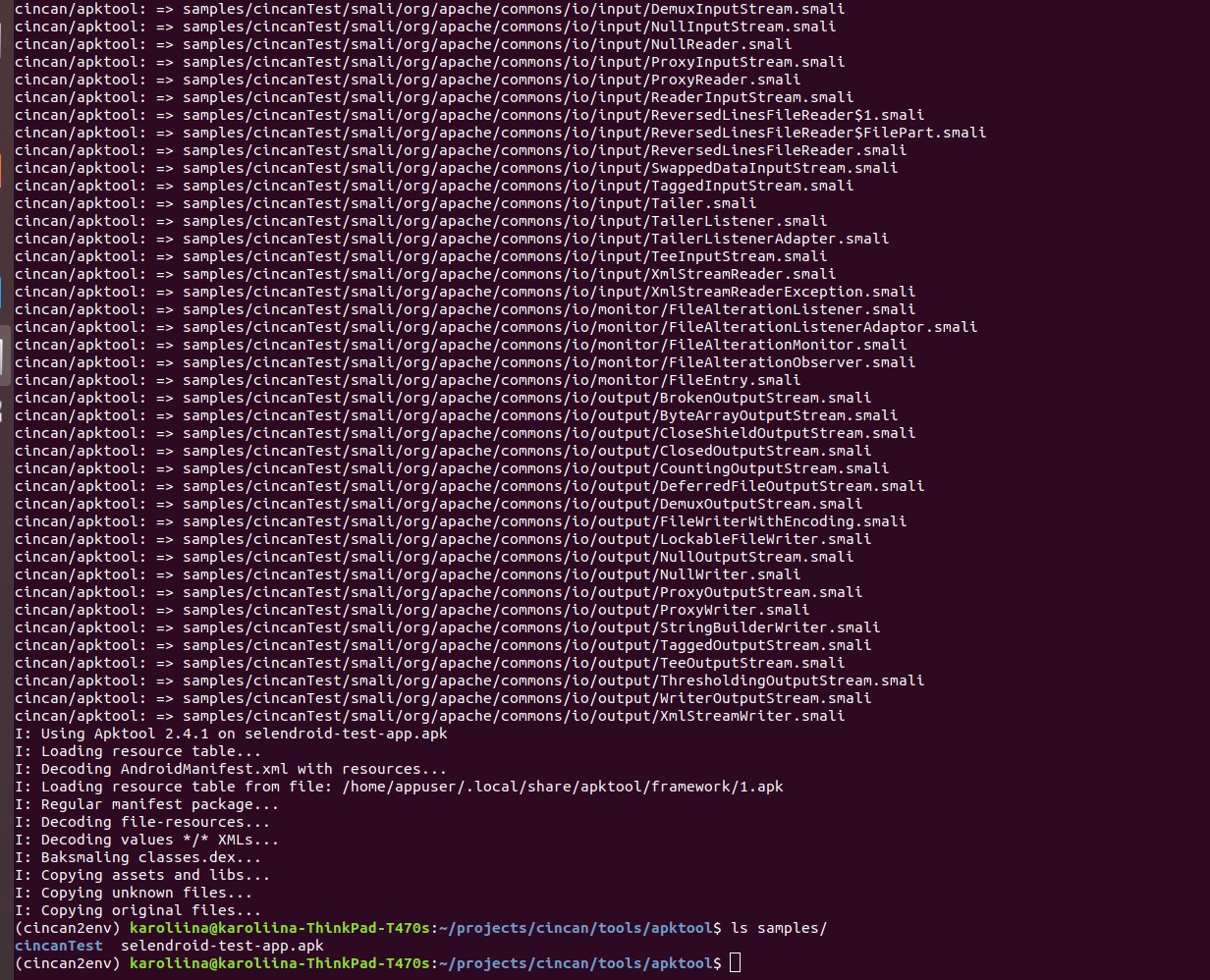
This is how it can be used when used with cincan tool
cincan run cincan/apktool d samples/selendroid-test-app.apk -o samples/cincanTest
Option d stands for decompile and -o defines the output folder where apk-files are decompiled
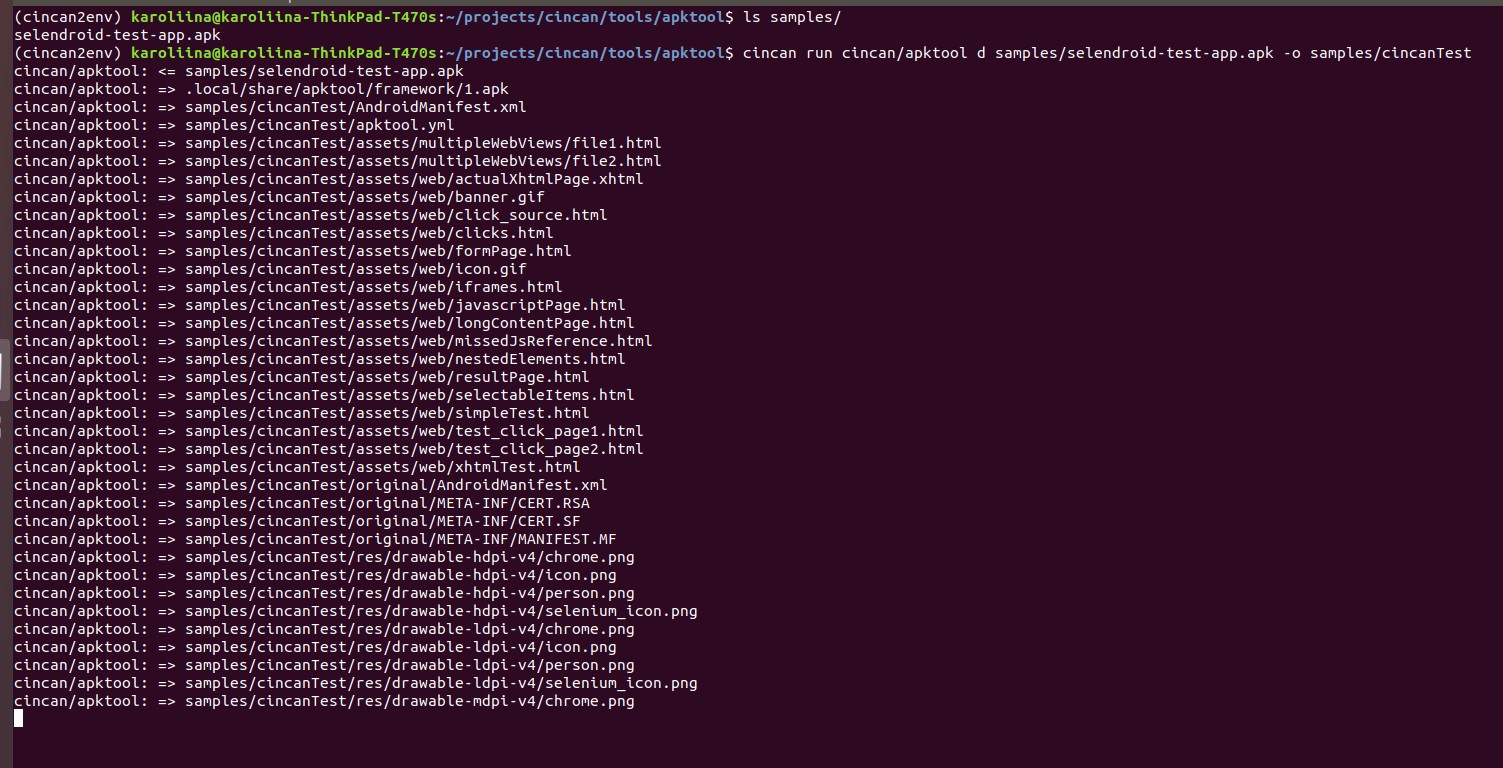
And the output can be found as follows:
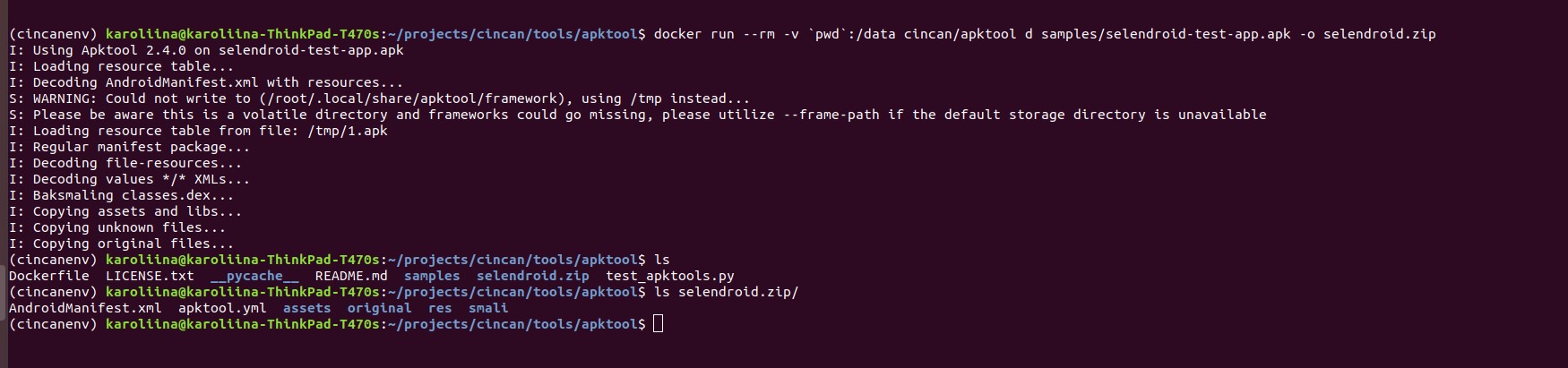
And without cincan it can be used as follows
$ docker run --rm -v $(pwd):/data cincan/apktool d samples/selendroid-test-app-apk - selendroid.zip
Please visit Apktool Github page to learn more about the tool and its other great features.
Other resources
A CLI tool called cincan is available to run these different kind of dockerized tools. Installation of this tool is enough - it downloads docker containers automatically when running selected tool. This tool can be installed from PyPi.
Take a look for many other tools in CinCan’s Gitlab repository!